
Content Visibility and Its Role in Demonstrating Compliance
Regulatory compliance is a crucial aspect of every organization’s operations. Failure to comply with industry-specific regulations can result in hefty fines and legal consequences. Achieving compliance can be a daunting task, however, especially for organizations with complex data landscapes and legacy systems. This blog post explores how content visibility can simplify regulatory compliance and help organizations achieve compliance with ease.
Understanding Regulatory Compliance
Regulatory compliance refers to the process of adhering to industry-specific rules, policies, laws, and regulations. These regulations can vary across industries and geographical regions. Some of the most common regulations include data privacy laws and industry-specific regulations such as:
General Data Protection Regulation
The General Data Protection Regulation (GDPR) is a regulation that sets rules on how businesses should handle the personal data of individuals in the European Union. It requires organizations to obtain explicit consent from individuals before collecting, processing, or storing their personal data and to provide them with access to their information. The regulation also mandates that companies report data breaches within 72 hours of their discovery.
California Consumer Privacy Act
The California Consumer Privacy Act (CCPA) is a privacy law that gives California residents the right to know what personal information companies collect about them and how it’s being used. It also requires companies to allow consumers to opt out of the sale of their personal information and to delete it upon request.
Gramm-Leach-Bliley Act
The Gramm-Leach-Bliley Act (GLBA) is a regulation that requires financial institutions to protect the privacy of their customers’ personal information. This includes safeguarding information such as account numbers, Social Security numbers, and credit scores.
Payment Card Industry Data Security Standard
The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards created to protect credit cardholders’ information. It applies to any business that accepts credit card payments and requires compliance with 12 specific requirements to ensure the protection of sensitive information.
Federal Risk and Authorization Management Program
The Federal Risk and Authorization Management Program (FedRAMP) is a government program that sets standards for cloud service providers hosting government data. It requires compliance with a set of security controls and provides a standardized approach to security assessment, authorization, and continuous monitoring.
Health Insurance Portability and Accountability Act
The Health Insurance Portability and Accountability Act (HIPAA) is a regulation that protects the privacy and security of individuals’ health information. It requires healthcare providers and related organizations to establish security policies and procedures to protect against unauthorized access to protected health information (PHI).
The Role of Content Visibility in Regulatory Compliance
Content visibility refers to the ability to track and monitor data across an organization’s systems and processes. Content visibility provides organizations with real-time insights into where content—particularly sensitive content like personally identifiable information (PII), intellectual property, customer records, financial data, and contracts—is stored, who has access to, and with whom they’re sharing it. Content visibility to this level of granularity enables organizations to identify compliance risks and take corrective actions. By leveraging the right technology and establishing a compliance-centric culture, content visibility can enhance compliance efforts and simplify the compliance process.
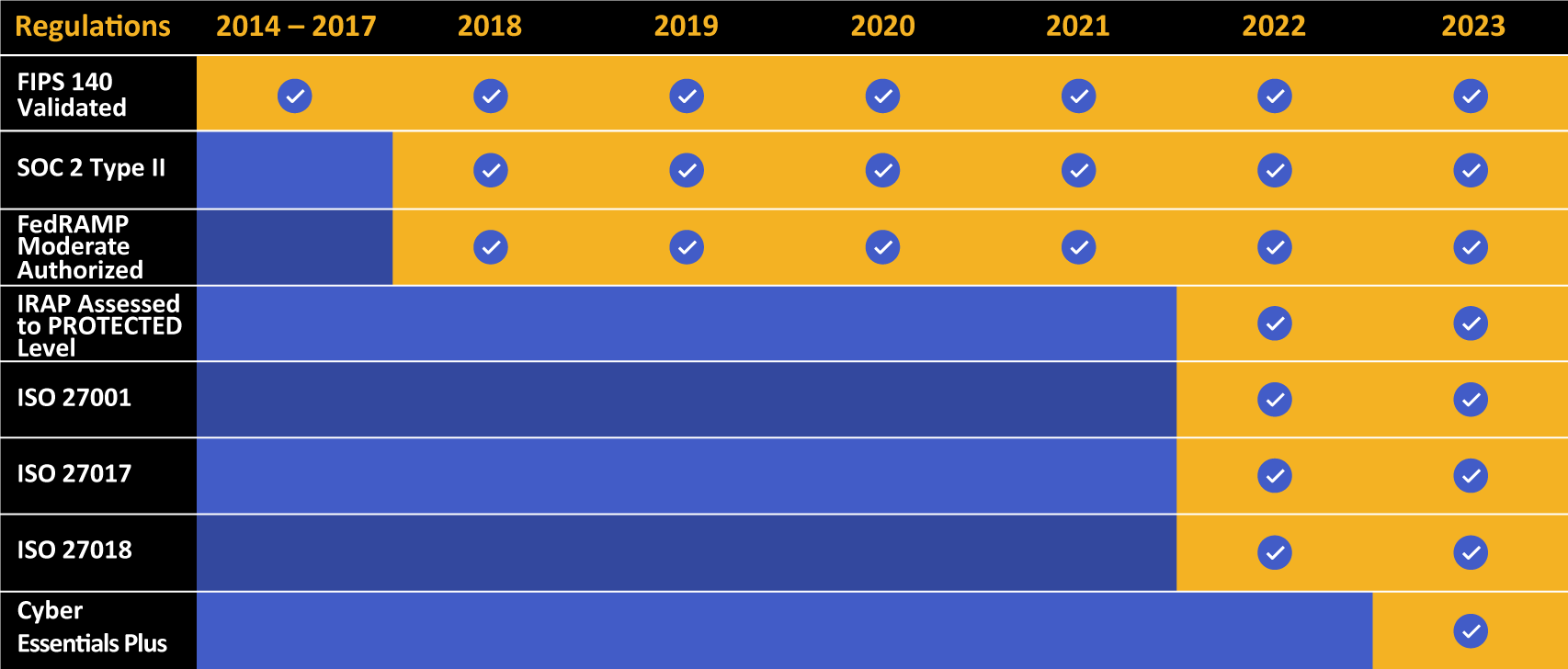
Kiteworks touts a long list of compliance and certification achievements.
Content Visibility and Data Privacy
Content visibility is becoming increasingly important for organizations that process, store, or handle sensitive information, especially PII. Regulations like GDPR and the Data Protection Act 2018 in Europe and the CCPA and many other state data privacy laws in the U.S. have put in place stringent requirements for how organizations handle PII. Content visibility tools allow organizations to monitor and control the flow of personal data within their systems, effectively mitigating the risks associated with data processing and handling.
To comply with data privacy regulations, organizations must be able to identify sensitive content like PII and ensure that such content is not mishandled or exposed to unauthorized access. Content visibility simplifies this process by providing a centralized view of all content within an organization’s ecosystem and enabling the identification of sensitive content.
Content visibility also facilitates transparency and consent in data handling, which are cornerstone principles of data privacy regulations. With content visibility, organizations can clearly communicate their data handling practices to data subjects, primarily customers, and obtain their consent for data processing.
Automating Compliance With Content Visibility Tools
Manual compliance processes can be tedious and time-consuming, leading to errors and noncompliance. Automated compliance tools streamline compliance processes by monitoring and tracking content across an organization’s systems and applications. These tools provide real-time alerts and enable organizations to generate compliance reports effortlessly. Content monitoring and tracking systems can be customized to meet industry-specific compliance requirements.
Building a Framework for Content Visibility
To achieve or demonstrate compliance, organizations must establish a compliance-centric culture by involving all stakeholders, from top-level management to front-line employees. Comprehensive policies and procedures must be developed to ensure compliance with industry-specific regulations. A centralized repository for all compliance-related data and documentation is essential to ensure easy access and management.
Content Visibility in Highly Regulated Industries
Highly regulated industries such as finance, healthcare, and legal face unique compliance challenges. For example, the healthcare industry must adhere to strict regulations to protect patient privacy, while the financial industry must comply with laws and regulations to prevent fraudulent activities and protect customer data. Content visibility can help these industries comply with their respective regulations by providing the necessary insights into their data landscapes, enabling them to make informed decisions and take corrective actions.
Overcoming Content Visibility Roadblocks
Implementing content visibility can be challenging, especially for organizations with complex data landscapes and outdated processes. Legacy systems and manual processes can hinder the implementation of content visibility, while security concerns and cyber threats can derail compliance efforts. Organizations can, however, overcome these roadblocks by implementing the right technology, employee training, and fostering a culture of cyber awareness.
Best Practices for Implementing Content Visibility
To implement content visibility successfully, organizations must conduct a compliance risk assessment, design and implement content monitoring strategies, and provide comprehensive training to employees. Fostering awareness of compliance and developing the necessary processes ensures that everyone is working toward the same goals. Other best practices include:
1. Define Clear Content Visibility Objectives and Goals
Before implementing data visibility, it is important to define clear objectives and goals. This helps organizations to determine what data needs to be visible, how it should be presented, and what specific outcomes they want to achieve.
2. Identify the Right Data Sources for Maximum Content Visibility
Organizations must identify the right data sources that are relevant to their goals and objectives. This requires understanding the data that is available, its reliability and completeness, and how it can be used to achieve the desired outcomes.
3. Use the Right Tools and Technologies to Achieve Content Visibility
Organizations must use the right tools and technologies to enable data visibility. This involves selecting the right data analytics software, database management systems, and data visualization tools.
4. Ensure Data Quality for Accurate Content Visibility
Data quality is critical for achieving accurate data visibility. This means investing in data cleansing, data standardization, and data governance practices to ensure that the data is accurate, complete, and consistent.
5. Establish Data Governance Practices to Maintain Content Visibility
Organizations must establish data governance practices to ensure that data is managed appropriately and in accordance with best practices. This involves defining roles and responsibilities, establishing data policies and procedures, and monitoring data usage and access.
6. Encourage Collaboration to Enhance Content Visibility
Content visibility requires collaboration across different functions and departments. This involves creating opportunities for cross-functional collaboration, encouraging data sharing, and facilitating communication between stakeholders.
7. Monitor and Measure Outcomes to Measure, Evaluate, and Improve Content Quality
Organizations must monitor and measure the outcomes of their content visibility efforts to determine their effectiveness. This involves tracking performance against objectives, measuring the impact of content visibility on business outcomes, and making adjustments as necessary.
The Benefits of Content Visibility Beyond Compliance
Content visibility can yield numerous benefits for businesses beyond regulatory compliance. An effective content visibility strategy helps businesses operate more efficiently, build trust with their customers, mitigate risk, and more. Let’s take a look at a few of these benefits.
Content Visibility Improves Operational Efficiency and Productivity
With content visibility, organizations can track and analyze their content inventory, identify redundancies, and automate processes, leading to reduced costs, streamlined operations, and improved productivity.
Content Visibility Creates Enhanced Data Governance and Risk Management Capabilities
By providing real-time insights into their content landscapes, businesses can identify potential security threats, data breaches, and fraudulent activities and take appropriate measures to mitigate the risks.
Content Visibility Provides Insights to Drive Business Growth
Through analysis of content usage patterns and behavior, businesses can identify new opportunities and user demands, optimize content strategies, and develop new revenue streams.
Power Your Content Visibility Capabilities for Streamlined Compliance With Kiteworks
Content visibility is essential for demonstrating compliance and protecting sensitive content. The Kiteworks Private Content Network provides organizations around the world and in every industry critical visibility into how data is used, who accesses it, and with whom they share it. Kiteworks’ content visibility capabilities also help businesses monitor and track all the file activities on their network and prevent unauthorized access to sensitive information.
With Kiteworks’ cutting-edge analytics tools, businesses can identify potential risks and take corrective action quickly. Kiteworks’ CISO Dashboard gives organizations an overview of their most sensitive content: where it’s stored, who’s accessing it, how it’s being used, and whether it complies with data privacy regulations. The CISO Dashboard empowers business leaders to make informed decisions about security and regulatory requirements.
Connectors to on-premises and cloud-based enterprise content management solutions like Box, Dropbox, Microsoft SharePoint, and OneDrive for Business ensure secure content access that’s monitored, tracked, and recorded. Enterprise application plugins like Microsoft Office 365, Salesforce, and iManage further improve content visibility and content security.
Auditing and reporting are important aspects of content visibility, and therefore regulatory compliance. Kiteworks provides a detailed and comprehensive audit log of all file activity, namely who sent what to whom, when, and how, that can be customized to meet specific regulatory needs. These logs can be fed into a connected security information and event management (SIEM) solution for threat detection, forensic analysis, legal holds and eDiscovery, and, of course, for regulatory compliance. Kiteworks in fact supports or helps organizations demonstrate compliance with several data privacy regulations and standards, including GDPR, HIPAA, FedRAMP, the Cybersecurity Maturity Model Certification (CMMC), Cyber Essentials Plus, International Traffic in Arms Regulations (ITAR), the International Organization for Standardization 27000 standards (ISO 27001) and many, many more.
Kiteworks protects PII and other sensitive information from unauthorized access with features like granular access controls, digital rights management, and end-to-end encryption. Organizations use these tools to set, control, and enforce who can access sensitive content.
To learn more about the Kiteworks Private Content Network and how it offers content visibility for your regulatory compliance efforts, schedule a custom demo today.
Additional Resources
- Blog Post A Guide to Information Security Governance
- Blog Post Protect Your Sensitive Content With These Ten Best Practices
- Video What You Need to Know About Kiteworks CISO Dashboard Capability
- Case Study AVL: Mitigating Risk With a Single, Secure File Sharing Platform
- Blog Post Regulatory Compliance and Cybersecurity Standards Drive Risk Management